Understanding the Data Protection Principles of GDPR:
To combat the challenges of rising threats in the digital era and after years of deliberations, GDPR was adopted by the European Union in 2016 and implemented in 2018. These regulations are exhaustive and provide a clear framework for adoption. Data processing and handling is no more an ethical responsibility but a legal requirement. The growth of data and dependency on data-driven business models have made it incumbent on all businesses, small or large, to comply with GDPR norms to varying degrees. Although businesses even in 2022 are facing challenges in dealing with the long and cumbersome GDPR legislation. However, the 7 GDPR principles are quick, simple, and lucid directives set out in GDPR that help businesses come a step closer to understanding and complying with European law.
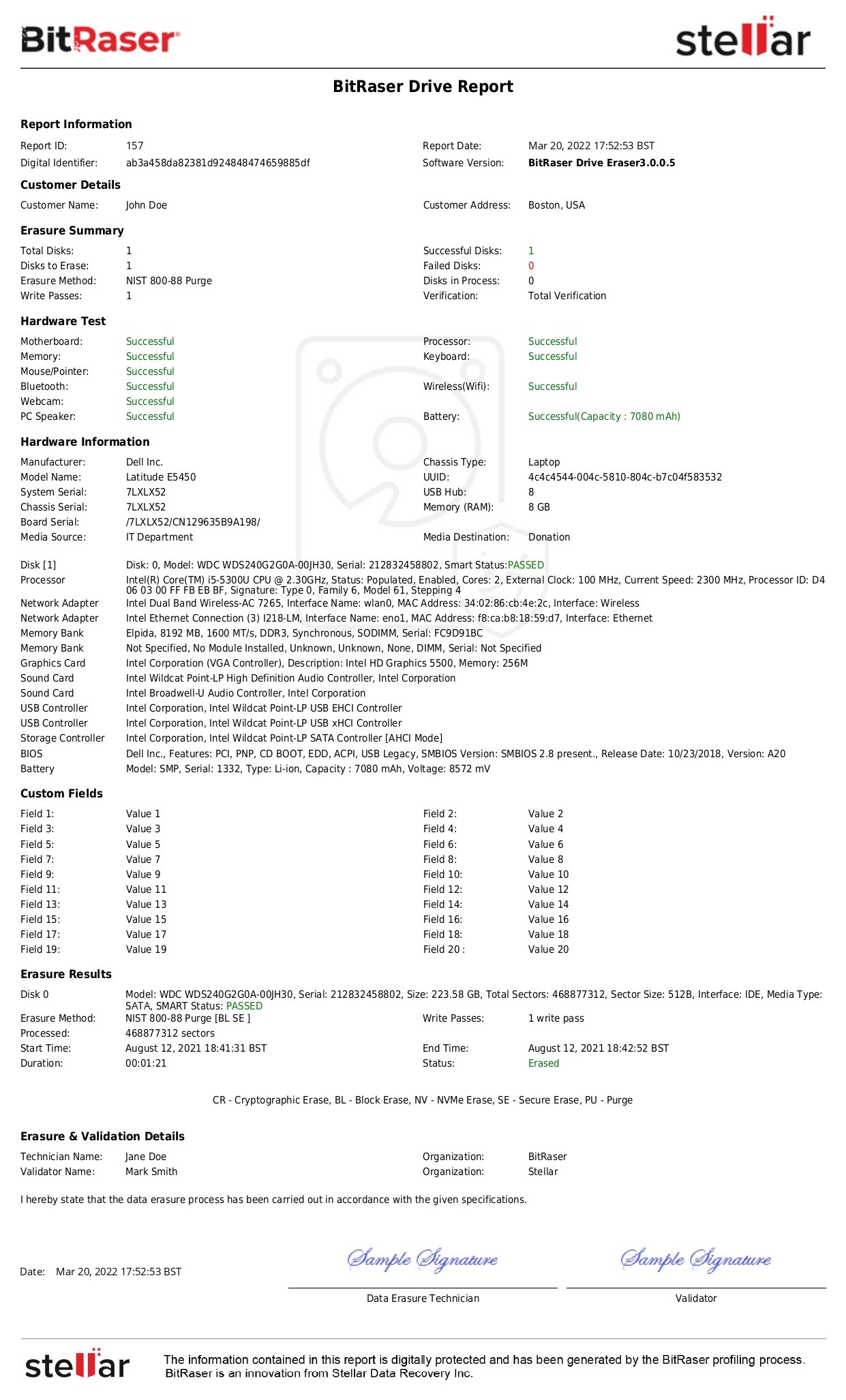
The 7 Data Protection Principles of GDPR are enumerated under Article 5, right at the beginning of the General Data Protection Regulation document. These privacy principles set the tone and direction of European law and send the message to data processors to focus on these 7 GDPR principles for compliance and prevent excessive fines. The significance of these principles lies in the fact that they have an overall influence on the entire GDPR law and impact the subsequent rules and obligations laid down in the document. Hence, any business looking to comply with GDPR must fulfill the obligations set under Article 5 of GDPR. The following is an insight into the 7 GDPR principles with examples of how businesses can achieve compliance:
Read Complete Infographic
GDPR Principle 1: Lawfulness, Fairness & Transparency
Simply put, it states that the data collection should be done legally; the collector must have a valid legal reason for collection and permission from the person whose data is being collected. It also means that the collected data will be used fairly and protect the person’s interest. The data collection process should be transparent so that data subjects (users) know why and how their data is collected and processed. For example, a company may take customers’ consent for sending them newsletters. Sharing the newsletter through this consent would be considered lawful, but to ensure that it is fair and transparent, the company must ensure that customers understand the scope and purpose of the newsletter is in their best interest. Fairness & Transparency would also mean that data collection is used for intended purposes and guided by the company’s privacy policies that are accessible to users. Fairness further demands businesses to give a choice to customers to pause the relationship.
GDPR Principle 2: Purpose Limitation
It means that the data being collected should be processed only for specified, explicit, and legitimate purposes, i.e., the data would be used only for the purpose it was collected for and cannot be used for any other purpose. For example, a customer gives consent to receive a newsletter from the company, and the company now sends discount promotions. This will be considered a misuse under the GDPR principle of ‘Purpose Limitation’ and a violation of privacy under GDPR.
GDPR Principle 3: Data Minimization:
The collection of data should be minimal, collecting only what is required to fulfill the obligations. Unnecessary details that serve no purpose to data subjects (customers) or businesses should be completely avoided. Considering our earlier example, if the company asks for details like job title or address for sending newsletters, it would be considered unnecessary and violates the data minimization principle.
GDPR Principle 4: Accuracy
The GDPR states that “every reasonable step must be taken” to securely erase or modify data that is incomplete or inaccurate. The data should be corrected, modified, and updated as and when necessary and inaccurate data that is no longer needed must be securely erased. For example, customers may switch jobs, change emails, or their contact details. If and when the customer updates his address or contact details, they have to be modified in company records to ensure the accuracy of the content. Thus, the company must ensure that every reasonable step is taken to update, modify or erase inaccurate customer data.
GDPR Principle 5: Storage Limitation
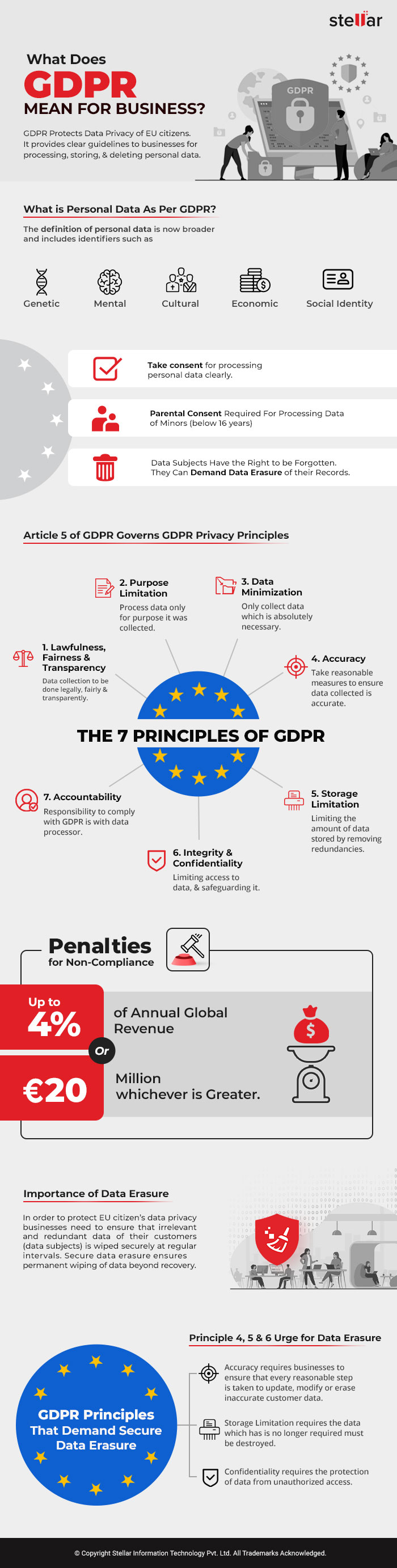
This principle states that the data which has reached its end of life must be destroyed. If the purpose for which data was initially collected has been met, then it should no longer exist in company records. This is an important privacy principle as any gap in this could often lead to breaches and disastrously impact any business. For example, suppose a company that publishes digital magazines had a customer who left their subscription without renewing it. In that case, the company no longer should be holding the customer’s financial information. It should completely wipe such information from the company records to uphold the GDPR privacy principle. Professional data erasure software can be used to wipe data completely without leaving any information trace. Such software generates tamper-proof reports of data destruction to serve as audit trails.
GDPR Principle 6: Integrity & Confidentiality
Derived from the Cybersecurity “CIA-Triangle” of confidentiality, integrity, and availability, this principle states that the data is correct and safe from external and internal threats, and access to the data is limited to only authorized people. For example, various businesses store sensitive data such as payment card information. E-commerce outlets, service providers, and online food chains store sensitive personal information like name, address, mobile number, and credit/debit card information. These businesses must adhere to principles of integrity and confidentiality by protecting customer details from threats and ensuring they are protected from unauthorized access.
GDPR Principle 7: Accountability
This principle requires organizations to take adequate technical and organizational measures to process the data of the subjects by adhering to all the six data protection principles as cited above and being able to demonstrate the process when requested.
Penalties and Fines:
Noncompliance with these seven privacy principles of GDPR attracts substantial fines and hampers the reputation of the business as well. Article 83 (5) (a) states that infringements of the basic principles for processing under Article 5 shall be subject to administrative fines up to EUR 20 Million, or in the case of an undertaking, up to 4 % of the total worldwide annual turnover, whichever is higher.
Follow Data Protection Principles to Accelerate GDPR Compliance
The compliance requirements mentioned in GDPR are all embedded within the 7 Privacy Principles. These principles have bestowed the data subject with immense power & protection while firmly placing the onus of security and accountability on the data processor’s shoulders. These principles embody the spirit of the GDPR regime and set the right tone at the very beginning of the GDPR legislation. The key is for organizations to understand what they mean and how they can apply these principles to their business and stay compliant. To ensure that a business is GDPR compliant, the organization must follow the above 7 GDPR Principles and implement them in their business as much as possible. To learn more about how data sanitization can help you in GDPR compliance, you can read our detailed article or contact us.