A Brief About the Privacy Act
Adhering to its commitments made to the Organization for Economic Cooperation and Development (OECD), Australia passed the Privacy Act in 1988. Also cited as the Privacy Act 1988, it came into effect in 1989. Since then, the Act has undergone several amendments to expand its scope. The Act outlines 13 Australian Privacy Principles (APPs) to be followed by Australian government agencies and certain private sector organizations, with an annual turnover of AUD 3 million, with regard to the promotion and protection of the privacy of the personal information of individuals. Hence, most small businesses do not fall under its scope.
However, this turnover limit does not apply to health service providers, personal information service providers, credit reporting bodies, operators of residential tenancy databases, businesses conducting protection action ballots, and other businesses listed by the government. Additionally, the Privacy Act includes the privacy component of the consumer credit report systems, tax file numbers, and health and medical research reports within its scope.
Non-compliance with the Privacy Act can attract huge fines and severe penalties, as outlined in a later section of the article.
Primary Objectives of the Privacy Act
The primary objectives of the Privacy Act are:
- To promote the protection of the privacy of individuals
- To recognize that protection of the privacy of individuals is balanced with the interests of entities in carrying out their activities or functions
- To provide the basis for nationally consistent regulation of privacy and handling of personal information
- To promote transparent and responsible handling of personal information by businesses and organizations
- To facilitate an effective credit reporting system as well as ensure the privacy of individuals
- To enable the free flow of information across the country's borders while maintaining the privacy of individuals
- To provide a means for individuals to complain about an alleged interference with their privacy
- To implement Australia’s international obligation concerning privacy
Key Provisions of the Privacy Act 1988:
Under the Privacy Act of 1988, provisions have been laid out for the collection, use, and protection of private information of individuals by government agencies as well as certain private sector organizations and businesses. These provisions are defined for both the federal and the state levels.
- Australian Privacy Principles (APPs): The APPs cover open and transparent management of personal information of individuals, a guarantee of anonymity, seeking of consent for the use and dissemination of personal information, notification for the collection of personal information, access to personal information, and correction of the information if the need arises.
- Personal Information: ‘Personal information’ under the Act includes the name, address, contact details, date of birth, gender, race, and sexual orientation of an individual. Health information, tax file numbers, credit history, electoral roll information, and history of old minor criminal convictions (spent convictions) also fall under this category of information that may be sought by the agencies.
- Consent for Information Collection: Personal Information may be collected only if it is necessary for the functions and activities of the agency. The individual has to give consent for the collection and use of the data. The individual must also be made aware of why the information is being collected, for what purpose it will be used, and who can gain access to this information.
- Protection Against Data Theft & Breach: Under the Act, data collecting agencies and organizations are required to ensure that the data collected, stored, and used by them are completely insulated against theft and breach. They’re also required to make sure that the data is not used for any other purpose except as originally specified.
- Setting Up of OAIC: Under the provisions of the Act, an Office of the Australian Information Commissioner (OAIC) has been established. The OAIC has also established certain rules and guidelines that are to be followed by agencies and organizations collecting private data of individuals for use.
Amendments to the Privacy Act
Since the enactment of the Act in 1988, several amendments and changes have taken place from time to time to expand the coverage of the Act. Some of the key amendments are as follows:
- 1990: Credit Reporting
The 1990 Amendment expanded the scope of the original Act to include the handling of consumer credit reports.
- 2000: Office of the Privacy Commissioner
In the 2000 Amendment, an Office of the Privacy Commissioner was established. The Privacy Commissioner was tasked with resolving the complaints of individuals who feel their privacy has been compromised.
- 2001: Private sector
Privacy Amendment Act of 2000 extended the scope of the Privacy Act of 1988 by extending the coverage of the Act to certain private entities in Australia. It also introduced 10 National Privacy Principles that would govern the collection of data, its processing, security, access, and disclosure.
- 2014: Major Reforms
Significant changes were made in the Act in 2014 with the introduction of the Privacy Amendment (Enhancing Privacy Protection) Act of 2012. These include the Australian Privacy Principles (APPs), for regulating government and private sector organizations in data handling, which replaced National Privacy Principle. It also gave provisions for comprehensive credit reporting, new laws on codes of practice for credit reports, and granting more powers to the Information Commissioner.
Key Requirements for Businesses and Organizations
The Privacy Act 1988 has laid down several provisions and guidelines, for businesses and organizations, which are required to be strictly followed by them.
- Provisions have been laid out concerning the collection, use, and protection of data of individuals as collected by businesses and organizations.
- Such information may only be collected if it is necessary for the functioning of the business and only after the consent of the individual has been obtained.
- Businesses are legally bound to protect the private information of their customers against theft, misuse, loss, unauthorized access, modification, and disclosure.
- If the businesses no longer require the information provided by the consumer, they are legally bound to destroy or de-identify the information.
- Businesses are mandated to implement adequate provisions to safeguard the information collected by them in compliance with the Australian Privacy Principles.
- The information of an individual must be made available to them if and when they request access to it.
Penalties for Non-Compliance of the Privacy Act
The penalties levied under the Privacy Act for breach of the provisions are severe and have been amended by the Australian government. Any entity covered under the act that is found to be in serious or repeated interference with or breach of privacy of an individual may be fined a maximum of $2.1 million.
As per the recent Online Privacy Bill dated 25 October 2021, the defaulting entity is now proposed to be levied a harsh fine of a maximum of $10 million, or 3 times the value of benefit accrued through misconduct and repeated interference with the privacy of citizens, or 10% of the entity’s domestic annual turnover.
Data Erasure: An Easy Way to Comply With Privacy Act 1988
The Privacy Act of 1988 has laid down several provisions for businesses and organizations to collect, use, and protect the data of individuals. They are bound to protect the personal information of their customers against any misuse, theft, unauthorized access, and disclosure. One of the major provisions of the Act is that if businesses or organizations don’t require the data, they are legally bound to destroy or de-identify such data.
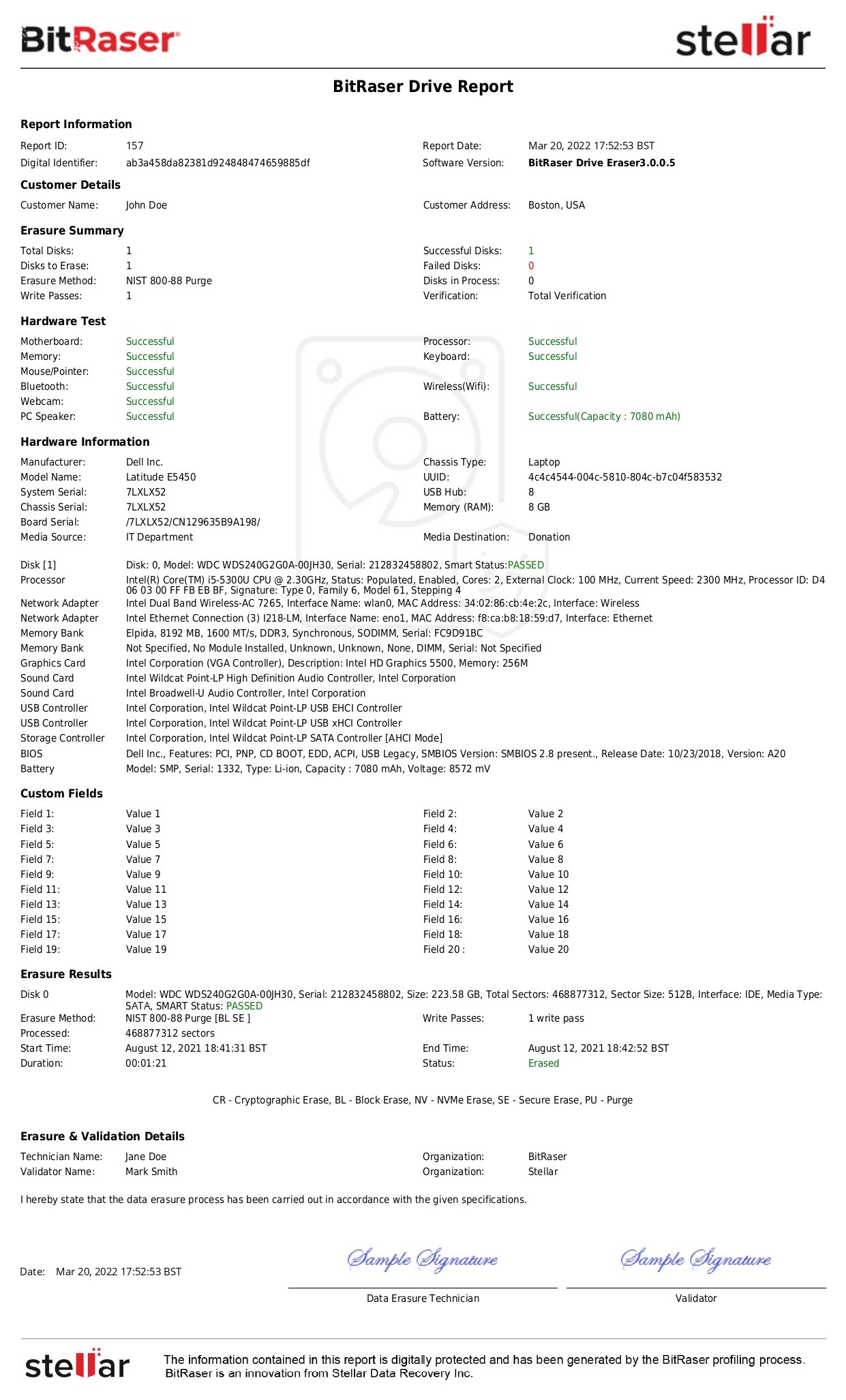
To solve this issue, organizations can take the help of a professional data erasure tool such as BitRaser to safely wipe the sensitive information at the time of IT asset disposal, helping them meet the data privacy obligations of the Australian Privacy Act.
To Conclude
Australia’s Privacy Act 1988 is one of the precursors of data privacy laws in the world that addresses the core concerns of protection and promotion of the right of an individual to their data privacy, data breach, and the obligation for businesses (data processors) to have informed consent. The Privacy Act 1988 intends to serve as an effective safeguard against the potential misuse of personal data shared with a private and public organization. Businesses and private organizations that fall under its purview must ensure that they comply with the provisions of the Act to avoid penalties and retain the trust of their clients and individual consumers. In addition, there is a major provision under the Act that mandates destroying of information, if not required. This can be easily complied with, by taking the help of a specialized data erasure tool.