Summary: The CCPA globally impacts organizations and overlooks how businesses collect and process personal data and demand changes in order to be compliant with the privacy laws of California. This article covers a comprehensive list of the top ten questions the chief information security officers must answer to check if their organization is CCPA compliant and provides practical recommendations on how businesses can achieve compliance as well as mitigate risk exposure.
The CCPA affects organizations not only in the Golden State but across the world. So, companies should expect a lot more interactions with users.
Given how California's Attorney General won't begin enforcing the law until July 1, 2020, now's the perfect time for chief information security officers (CISOs) to prepare for compliance-related requests from business customers and end-user requests submitted directly to their respective businesses. In the process, security managers can find gaps in their CCPA compliance, and avoid fines and lawsuits for violating the regulations.
Without further ado, here are the top 10 questions tech executives should be in a position to answer before the enforcement deadline is over:
1 - Does Your Company Fall Under the CCPA's Purview?
This question is relatively easy to answer. Does your organization:
- Collect personal data on California citizens?
- Generate more than $25 million in revenue annually?
- Handle personal information for 50,000 Californian people, households, or devices.
- Make at least half its revenue selling data on California residents.
If you answered yes to any of the questions, your business falls under the California Consumer Privacy Act.
According to the IAPP, over 500,000 companies must comply with CCPA, 400,000 of which are situated in states other than California. A study indicates that 75 percent of all California businesses and international firms gathering data on California citizens must comply with the CCPA too.
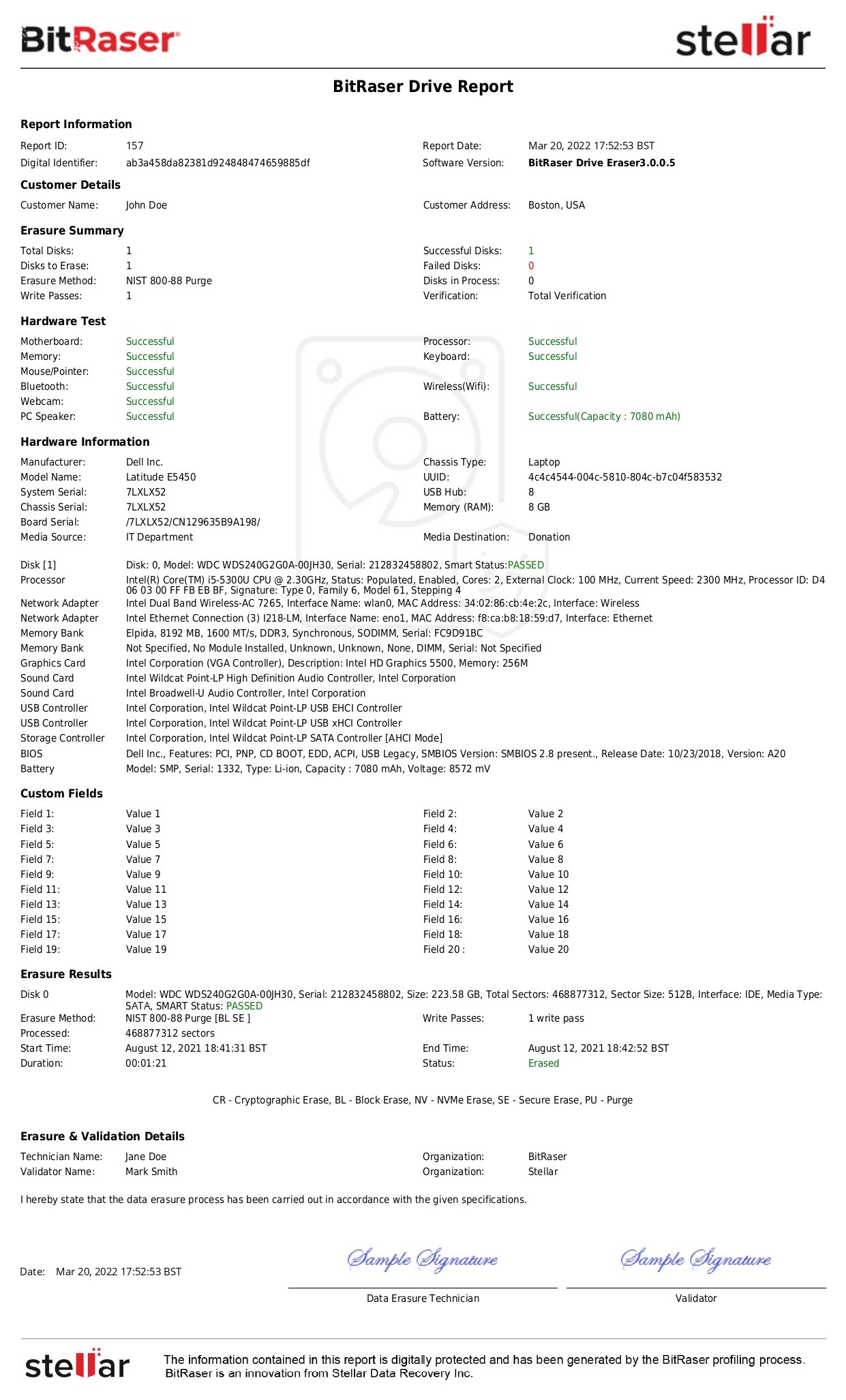
2 - Must You Be Compliant with Both the CCPA and GDPR? Or Is the Latter Enough?
The GDPR became law in May 2018. To date, GDPR violations have cost businesses millions of euros in fines, including whopping £99 million and €50 million judgments against Marriott and Google respectively in 2019. While CCPA requirements are comparatively relaxed, some aspects go further than the GDPR. Consumers, for example, can file lawsuits against organizations thanks to the broader definition of private data under the CCPA.
So, even if your company is in compliance with GDPR, it may not meet CCPA standards. Focus on updating your privacy policy and customer contracts. Understand the incremental changes demanded by the CCPA guidelines. Make your business future-ready by allowing users to access and control their personal data regardless of location.
3 - Do CCPA Regulatory Requirements Interfere with Your Business Objectives?
Your business must process personal information to capture the target audience through complex digital marketing efforts. Closely monitor these activities for disclosure, consent, and transparency. Digital marketing is impossible without personal data. If your company wants to work with a third-party marketer for a data sale, consumers can opt out of the sale of their data under CCPA law. Businesses should therefore identify a sale and apply suitable marketing practices.
4 - Is Your Company in Compliance with CCPA?
A December 2019 survey found that 52 percent of companies would not be CCPA compliant by January 1, 2020. In fact, those estimates were rather optimistic. Businesses claiming to be compliant were not truly compliant. Only larger businesses were somewhat prepared to handle the fallout from CCPA implementation. A major drawback was the broad view of personal data that the CCPA adopted. Under the Act's provisions, the contents of a leave request email from an employee could be construed as privacy or personal data.
Also, many businesses mistook using a CCPA-compliant vendor for handling sensitive information as being CCPA-compliant themselves. Amidst all the confusion, organizations did not modify their websites. At its core, the CCPA was too new a law and still changing. Familiarize yourself with the CCPA guidelines and work on processes that give consumers their data within the 45-day window. Check the earlier section on 'Obligations for Organizations/Businesses' for a better idea of how to proceed. Remember, your business is responsible for your data as well as its compliance.
5 - Are You Aware of Your Risk Exposure?
Most businesses understand what data they keep, where they keep it, and how it is protected. If you don't, begin a data mapping project. Maybe your business is accidentally not compliant since you aren't aware of a section within your organization that is gathering and maintaining protected data.

Also, it's hard to say for sure whether your business is 100% compliant given how new the CCPA is. Companies are constantly changing their data collection methods and business processes. The law itself is evolving thanks to modifications proposed by the Attorney General. For parts of the law that are ambiguously worded, the case might end up in the courts. Still, your business should err on the side of caution since you won't get definite answers right now.
6 - How Do You Let Others Know That You Are CCPA Compliant?
Apart from lawsuits and fines, the lack of CCPA compliance may lead to significant business loss. So, get your business' privacy team to analyze the CCPA. If you have prior experience handling GDPR requirements, use it to lay the groundwork.
Decide on your approach to compliance. For example, you may try the 'superset' - a single centralized system tracking both CCPA and GDPR privacy laws. Take the highest common denominator - GDPR allows 30 days for responses, CCPA 45. So, respond to every request within 30 days.
Update your data management systems to include CCPA requirements. Also, publish details about your company's CCPA processes on the official website. Create a data processing system for both new and existing users to sign. Explain your obligations under CCPA and how your business will protect its data.
7 - How Much Will CCPA Cost You?
Estimates suggest:
- Smaller businesses with 20 employees or less must pay $50,000 in initial costs
- Mid-sized firms with 20 to 100 employees must spend $100,000
- Companies with up to 500 employees will pay $450,000
- Organizations with over 500 employees must spend $2 million
CCPA is not an opportunity to pad your budget, nor incite fear, doubt, and uncertainty. Your business should treat CCPA as a new operational program for the company rather than a standalone annual budget item.
8 - Does CCPA Raise Privacy Awareness In Your Company?
CCPA is helpful for improving your business' culture of awareness. The regulations set, up good data governance and privacy awareness as the new gold standard. Educate your leaders about integrating this program into the organization's business processes instead of tacking it on as a mere afterthought.

Companies can increase awareness by:
- Updating their websites
- Reconsidering data collection strategies
- Implementing systems to track and delete data
- Reviewing contracts with business partners and vendors
CCPA also increases authentication awareness, thanks to its cybersecurity component to compliance. This prevents online identity thieves from accessing information about true data subjects and trolls from duping businesses into deleting all details about a certain user. Earlier, when customers canceled their accounts, businesses would retain backups of their data and simply reinstate it when the cancellation request turned out to be fraudulent. Now, however, the new privacy law calls for the data to be deleted in its entirety.
9 - Can You Avoid CCPA Hassles by Paying the Fine?
Many businesses find the wait-and-see approach to CCPA tempting. After all, enforcement won't begin until July, and even then, regulators will probably target the biggest offenders first. In fact, many CISOs consider fines less problematic than preparing for CCPA compliance. That is untrue since CCPA allows California citizens to file lawsuits individually in the event of a breach. Each privacy violation racks up fines of up to $7,500. So, if 1,000 Californians visit your website and complain about the lack of opt-out buttons and notifications, you might be looking at a total penalty of $7.5 million.
Breaches cost your business $750 for each lost record. On top of that, California consumers get to sue your company as well.
So, CCPA compliance may be expensive but it is nothing compared to the huge fines your firm has to pay for non-compliance. Since GDPR went into effect, 160,000 breaches have been reported in the UK and Europe, resulting in fines worth $448 million.
The potential for private litigation under CCPA makes the cost a lot higher, and the situation is compounded by the fact that California ranks among the worst states for businesses to face lawsuits.
Of course, this doesn't mean your business is under threat from CCPA. But law firms and lawyers will pay more attention to consumer protection and data privacy than ever before.
10 - Is CCPA the End or Just the Beginning for Privacy Laws?
Other laws are already in progress. Depending on the impact of CCPA, several states will take action. Thus, businesses and tech executives need to prepare for a crisscross of laws, similar to how data breach notification laws vary from one state to another. To know more about other data privacy laws in the US, refer to our comprehensive article US Data Privacy Laws.
Federal law is necessary to prevent states from introducing their own interpretations and variations of the CCPA. However, the first order of business is a consistent approach to personal and private data usage in the US.
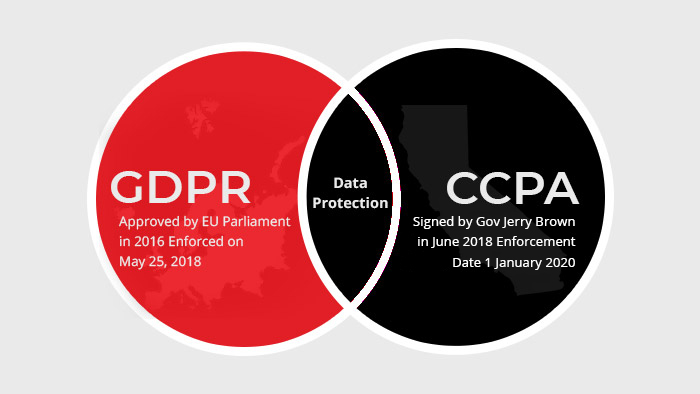
A secure Data Eraser Software helps comply with CCPA Regulations and prevent data breaches.