Commercial printers such as enterprise or workgroup-class printers, typically installed in large offices and connected over a local area network, are used for printing large volumes of data in a multi-user environment. These commercial printers comprise a dedicated (removable) hard drive to store scanned images, PDFs, and other types of documents for printing. A non-volatile memory such as traditional platter-based storage (HDD) or flash storage (SSD) allows these workgroup-class network printers to copy the documents without spooling them.
Multi-function Printer or MFP is another category of printer for dispensing multiple tasks such as printing, scanning, faxing, and email. MFPs serve a similar utility like the workgroup-class printer, at a lower volume, so they might also have a dedicated hard drive for data storage. Ricoh, HP, Epson, Dell, Brother, Canon, Xerox, and Lexmark are some of the leading manufacturers of commercial printers and MFPs.
Data Vulnerabilities on Printers with Hard Drives
A basic understanding of the printer hard drive data storage mechanism is necessary to comprehend the potential data vulnerabilities associated with such printers. In layman's terms, the printer hard drive keeps storing and queuing the printing tasks in a circular buffer, i.e., sequential units of the memory in a circular order, without deleting the previous tasks. It starts overwriting the previous tasks only after filling up the memory.
This fact means the data stored in a printer's hard drive can persist in the media for days and even weeks. This data comprising print jobs, fax, copy, scan, address book, etc. is vulnerable to a cybersecurity breach or leakage due to improper disposal of the equipment. The following section outlines the threat actors:
Printer Data Breach – Threat Actors & Scenarios
The following are the two main data breach & leakage scenarios concerning printers with hard drives:
- Network Breach
Commercial printers serve multiple users on the organization's local network, also connected to the Internet. This "network" is often the doorway for hackers to eavesdrop, who can also hijack the printer and other client machines in the network.
Imagine this scenario; the HR department in an organization stores the employee onboarding forms on the printer hard drive to allow remote populating and printing of the forms. These forms continue gathering the personal data of the users until the hard drive is "flushed". Meanwhile, the HR personnel receives a few resumes as email attachments with malicious code that triggers only on the printer OS environment.
This malicious code sneaks past the malware program on the client machine and gets installed on the printer's hard drive. The malware now eavesdrops on all the connected nodes on the network and steals the sensitive documents stored in the printer without detection, leading to a data breach incident – detected & reported way down in the future.
This situation sounds scary, but it is possible and makes for a big chunk of print-related data breach incidents. As per Global Print Security Landscape, 2019 report by Quocirca, 60% of businesses in the UK, the US, France, and Germany suffered a print-related data breach in 2018, incurring losses to the tune of USD 400,000. Aside from reinforcing the upfront protection against hacking or malware through firewalls and system upgrades, you could also consider setting up a deliberate and routine practice for the permanent removal of unwanted data from the printer's hard drive. You can explore the printer's built-in function for clearing the data or use the data erasure tool for systematic & permanent wiping. Read the following sections on the concept of media sanitization and data erasure technology for wiping clean the printer hard drive.
- Improper Disposal of Printers
Printer data leakage may also happen due to "improper sanitization" of the hard drive when transferring the printer's custody, as we explain next. There are several "exit points" in the printer's lifecycle or any other electronic hardware, including computers, when the artifact changes custody (ownership). This change of device ownership necessitates deliberate media sanitization to avoid exposure to the sensitive or confidential data stored on the device.
Media sanitization means the systematic destruction of the data stored in a media such that it becomes unrecoverable using any tool or technique. Formal media sanitization methods focus on safeguarding redundant data against the risks of exposure, misuse, and even penal actions.
For example, a commercial printer acquired on a lease may accumulate a large amount of sensitive data in the hard drive. The user or custodian organization is at immediate risk of data leakage if it fails to sanitize the printer's hard drive before returning the printer. Another data leakage situation may crop up due to the disposing of an old printer without sanitizing it. For example, selling a used printer to the highest bidding vendor, donating it for charity, exchanging the device, or discarding the hardware for recycling are a few exit scenarios that can risk the exposure of sensitive data. Anybody in possession of the printer can extract (steal) the data from the hard drive, exposing sensitive documents, faxes, copies, and print jobs.
Data Erasure Technology – A Failsafe Solution to Wipe & Sanitize Printers
There are several different media sanitization technologies in mainstream usage, widely categorized as Shredding, Degaussing, and Erasure. Shredding involves the physical destruction of the hardware into smaller pieces such that the storage media is rendered unusable to prevent data retrieval. Shredding turns the hardware into toxic e-waste with no residual value for reuse or resale. Further, shredding is typically done off-site due to financial and logistic constraints, so the threat of data leakage remains looming while the printer hard drive is in transit to the shredding facility and until shredded.
Degaussing destroys the data by demagnetizing the magnetic storage media such as a hard disk drive. The technique turns the storage hardware inoperative, as the magnetic field is neutralized, and therefore, the media cannot store the data. Degaussing is an ineffective method to sanitize emerging magnetic storage media and flash memory-based storage devices. As per NIST SP 800-88 Guideline, "existing degaussers may not have sufficient force to degauss evolving magnetic storage media and should never be solely relied upon for flash memory-based storage devices or magnetic storage devices that contain non-volatile non-magnetic storage". Degaussing like Shredding results in e-waste generation, and it also doesn't work on flash storage media such as solid-state drives.
Data Erasure (also known as data wiping) involves overwriting the existing data with unique binary patterns to mutilate and desensitize it. The data erasure technique turns the overwritten data illegible to any kind of read or extraction tools or techniques without affecting the storage media (hardware). The erased media can be reused or monetized through resale and therefore retains its life stage value like a PC can be reused after fresh OS installation. The data erasure technique can sanitize hard disk drives, solid-state drives, and any other media in an operable state, and it does not generate any e-waste.
Therefore, data erasure or wiping makes the best choice for printers having a dedicated hard drive, mainly including enterprise or workgroup-class devices and MFPs.
The good news is that there are professional data erasure software tools that can provide an easy (DIY), efficient, and compliant method for wiping the hard drives and SSDs used inside a printer. These software tools can permanently erase the hard drive, as per the prevalent data erasure standards, and ensure that no data recovery tool or technique can recover the wiped data. Professional data erasure software also provides documented proof to attest to the wiping process and its efficacy to fulfill the global regulatory norms for data protection.
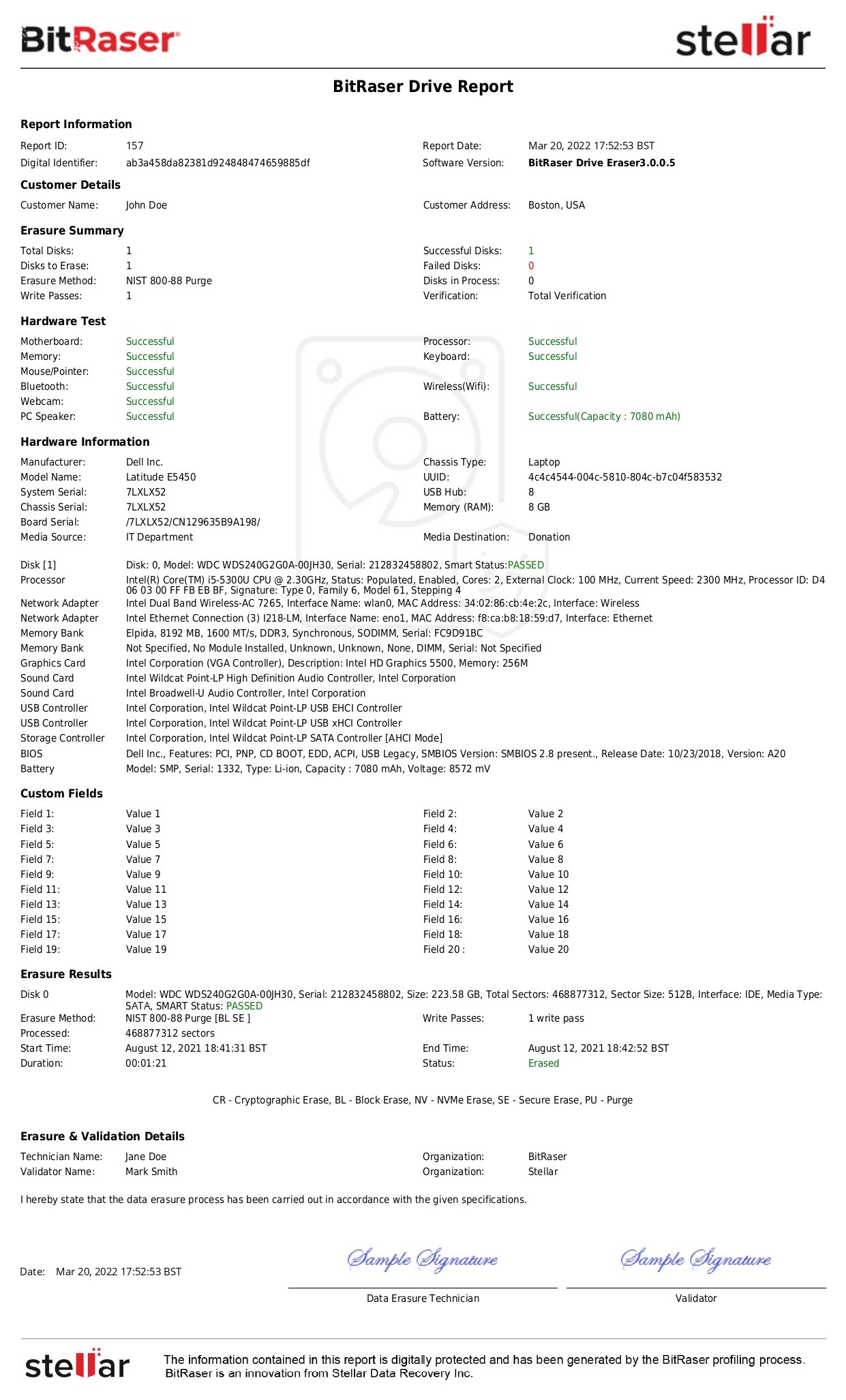
For example, you can try BitRaser Drive Eraser, a commercial data-wiping software designed for erasing the hard drives and SSDs used in printers, laptops or desktops, workstation computers, servers, etc. It permanently wipes the storage media based on international standards such as NIST 800-88 and DoD 3 & 7 passes. It generates tamper-proof certificates and reports of erasure to serve regulatory mandates.
Curious About How to Wipe the Printer's Hard Drive?
Please read our detailed & easy-to-understand software KB on how to erase your printer's removable hard drive using BitRaser Drive Eraser. The software can start erasing the hard drive in about 10 minutes, thereby protecting your data against risks of breach and leakage.