The NIST SP 800-88 Media Sanitization guidelines, released by the National Institute for Standards and Technology (NIST), are a set of instructions for effectively sanitizing storage devices and other electronic media. Widely adhered to by the U.S. government and corporates, these guidelines act as the benchmark for enterprises to drive their ‘media sanitization programs’, with defined techniques and control over sanitization and disposal decisions. NIST 800-88 assists every organization looking for assistance with decision-making for the sanitization, disposal, reuse, or migration of media and information. The National Institute of Science and Technology (NIST) provides technical leadership for the United States' measurement and standards infrastructure and defines media sanitization as:
"The general process of removing data from storage media, such that there is reasonable assurance that data may not be easily retrieved and reconstructed."
NIST SP 800-88 Rev.2, Guidelines for Media Sanitization, effective Sep 26, 2025 has replaced NIST SP 800-88 Rev.1 (2014). To learn more about the revisions, read NIST SP 800-88 Rev2 Media Sanitization Guidelines.
During the transfer or disposal of storage media, it is imperative that the deleted data from storage media (whether residual magnetic, optical, electrical, or any other form) is not recoverable. Storage media sanitization refers to a process of removing data with the assurance that the data cannot be retrieved or reconstructed. Media sanitization is crucial to maintaining data privacy standards and the smooth exercising of privacy controls. There have to be defined means and mechanisms to prevent sensitive information leakage across the IT asset lifecycle.
What is the Need for Media Sanitization?
As per NIST 800-88 guidelines, media sanitization is a critical element in maintaining data confidentiality. Organizations need to exercise proper control of sensitive 'confidential information' to avoid data leakage due to improper disposal of storage media or improperly wiped refurbished media. This practice is essential to protect against data leakage of Personally Identifiable Information (PII) based on reference 2.3 of the NIST 800-88 Media Sanitization guidelines. Organizations are required to follow data protection laws, regulations, and mandates governing the management of PII (Personally Identifiable Information). They may also have obligations to protect PII as per their policies, standards, or management directives. Violation of data protection laws can result in penalties or civil/criminal proceedings for organizations.
What is the Scope of Media Sanitization?
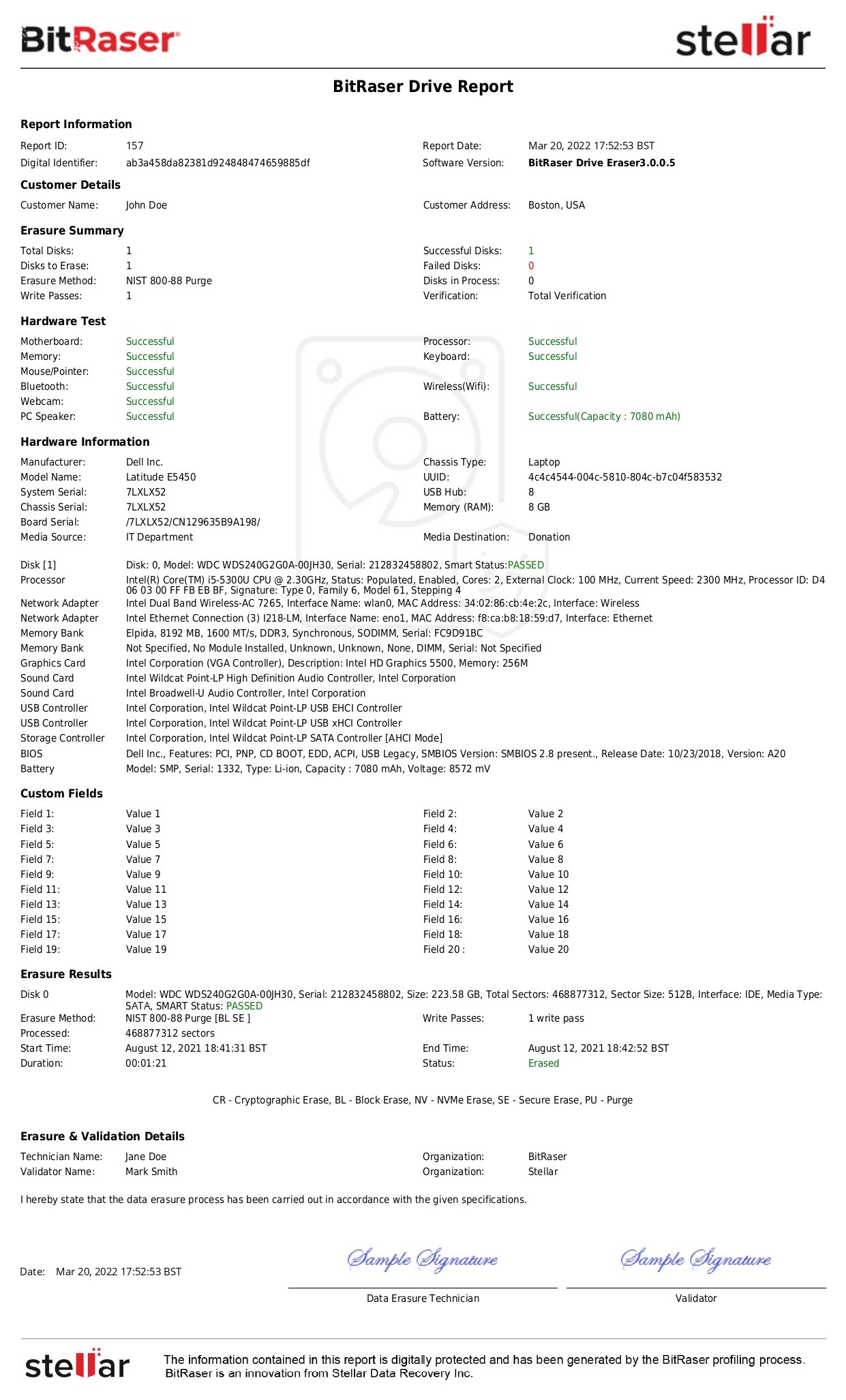
NIST 800-88 guidelines for media sanitization & data protection state that the sanitization operation is to be performed on complete data stored on the media, as it may be difficult for media sanitizers to differentiate the sensitive data, in particular. NIST refers to the ultimate sanitization and/or disposition of media and information. Partial data sanitization is risky and not approved as per NIST 800-88 standard guidelines. NIST 800-88 Revision 1 covers all kinds of storage media, whether hard drives, solid state drives, optical discs, flash memory, or paper media, irrespective of data sensitivity levels. These guidelines indicate three basic operations: NIST Clear, Purge, and Destroy, which aim at preventing the retrieval of the data by an unauthorized person or party. It is useful throughout the life span of the media, from active use to disposal. Risk management and meeting regulatory requirements are crucial principles of these guidelines. In order to guarantee that personal data is well and irretrievably erased, organizations must record and validate the sanitization process. After sanitization, a certificate of media disposition (also called a Certificate of Destruction) should be made available for each media to confirm it is sanitized. Certification of Destruction (COD) is a paper or electronic document of the sanitization process that has been taken.
Once the decision is made for media sanitization w.r.t media sanitization method, the type of media, and environmental impact consideration, the question arises as to who should be the decision-maker. Who will determine what, when, and how the data is to be sanitized?
Who is Responsible For Secure Media Sanitization?
As per NIST 800-88 Media Sanitization guidelines, the process should be done by different positions in an organization. Data owners have the principal responsibility of erasing all records from the media before it is recycled or recycled. IT and security undertake the responsibility of sanitizing data using the most suitable methods, which are Clear, Purge, or Destroy, depending on the level of sensitivity of the data. Compliance officers make sure that these processes observe the set regulations and guidelines, while asset managers oversee all the IT asset sanitization procedures across the lifecycle. In outsourced media sanitization, responsibilities lie with the third-party vendor, who is supposed to adhere to the stipulated procedures and produce certification when through. All in all, these roles guarantee that sensitive information does not leak out from the media and that it is wiped off as permanently as possible.
NIST 800-88 Media Sanitization Rev 1 guidelines help categorize and assign media sanitization roles and responsibilities as per the following:
- Data Owners, IT Security Teams, Compliance Officers, Asset Managers & Third Party Vendors - Example Chief Information Officers, Information System Owners, Information Owners, System Security Managers, Privacy Officers, & Users
- Determining and categorizing security as per compliances - SOX, HIPAA, PCI-DSS, EU-GDPR, etc.
In the decision process of media sanitization, the confidentiality of the information plays a key role, whereas the type of media plays a secondary role. Decision-makers decide upon the kind of sanitization on the basis of individual requirements. The decision for the safe disposal of leased or end-of-lifecycle IT assets is made to prevent data breach situations and meet legal compliances. Physical destruction methods are ruled out as they are not environment-friendly. Instead, decision-makers prefer media sanitization using data erasure software.
NIST 800-88 Media Sanitization Techniques & Methods
Commonly used media sanitization methods are data erasure, degaussing, shredding, factory resets, data deletion, reformatting, and physical destruction.
- Techniques like shredding, factory resets, data deletion, and reformatting are incomplete methods of media sanitization and can leave traces of data behind. Read More about the difference between deletion & data erasure
- Degaussing eliminates the magnetic field from the storage devices, thus rendering the data available on these devices unrecoverable.
- Data erasure uses an overwriting technique of overwriting the media with zeroes and ones to destroy the available data on storage media, rendering the media usable for future use. Data Erasure helps promote the sustainability objectives of recycling and reuse.
Media Sanitization Methods as per NIST 800-88 Guidelines
NIST guidelines specify the media sanitization techniques vis-à-vis the type of data storage media, including magnetic storage, flash memory-based media, RAM and ROM-based storage devices, etc. The table below summarizes the recommended “minimum sanitization” needs for different storage media types against the specific techniques (or methods) as follows:
|
Media Type
|
Clear
|
Purge
|
Destroy
|
|
Magnetic Media - ATA Hard Drives, Tape drives, SCSI Drives, SATA, PATA drives
|
Overwrite using validated overwriting technologies or methods or approved software
|
Secure Erase, Degaussing, or Cryptographic Erase (CE) is considered under NIST Purge
|
Incinerate, Shred, Pulverize, Disintegrate is considered a destruction method
|
| Flash Memory-Based Storage devices - ATA SSDs, SCSI SSD, USB, Memory Cards |
Overwriting media using one pass of writes with a fixed data value using the software. Secure Erase ATA command is also considered |
Block Erase, Cryptographic Erase through TCG Opal SSC, or Enterprise SSC interface to issue a command to change all Media Encryption Keys (MEK) |
Incinerate, Shred, Pulverize, Disintegrate is considered a destruction method |
|
CDs/DVDs
|
N/A
|
N/A
|
Shred and disintegrate - reduce to particles |
|
Mobile Devices - Apple iPhone, iPad, Android devices, Windows OS devices, and all other mobile devices, including tablets
|
iPhone: Overwrite with one pass along with CE
Android & other device: Factory reset
|
iPhone: Same as Clear
Android & other device: Secure Trim command, Cryptographic erase (CE), Secure Erase
|
Incinerate Shred Pulverize Disintegrate
|
NIST SP 800-88 Best Practices for Media Sanitization
This section outlines the media sanitization best practices based on NIST SP 800-88 recommendations, as follows:
1. Consider the risks of partial media sanitization [Section 2.8]
Typically, organizations sanitize the complete data stored on a media, i.e., perform full sanitization. However, some situations might require only partial media sanitization. For example, adherence to modern data privacy regulations might require an organization to retain the data of its new customers but is mandated to erase the data of its churned customers. NIST SP 800-88 guideline cautions on the potential risks of partial media sanitization due to its technical challenges and risks, such as spillover of sensitive data on the drive’s unwiped sectors.
2. Identify media sanitization needs and methods in advance [Section 4.1]
The guide states that media sanitization needs and media types should be identified before reaching the disposal phase in the IT asset management lifecycle. The type of storage media is a fundamental factor in determining the right data destruction method and the overall sanitization duration. The guide recommends taking the help of storage hardware vendors to identify the storage media, typically documented in a “statement of volatility.” However, organizations need to exercise due diligence while reading the statements, considering the vendor-specific variances in the provided details.
3. Identify the data confidentiality levels [Section 4]
NIST guidelines mention the “data confidentiality level” as a crucial factor in supporting effective data destruction and decision-making. Further, it recommends maintaining a mapping of the type of data, based on its confidentiality level, stored on the devices to facilitate effective and efficient media sanitization. NIST emphasizes using the procedures described in Federal Information Processing Standard (FIPS) Publication 199 to determine the data confidentiality level.
4. Determine the security categorization [Section 4.2]
Security categorization is essentially a way to classify a system’s confidentiality based on the FIPS 199 definition in the NIST SP 800-60 Rev. 1. Security categorization provides a crucial input to the system owner for designing a media sanitization process that meets the organization’s needs and standards for data protection. NIST 800-88 Media Sanitization guidelines mention the need to revisit the security categorization, stating that “security categorization is revisited at least every three years (or when a significant change occurs within the system) and revalidated throughout the system’s life.”
5. Consider the media control and access aspect [Section 4.4]
The media sanitization decision is also influenced by the entity having control over the outgoing storage media. The device ownership might change or remain the same based on specific circumstances, which should be considered while choosing a sanitization method. For example, media being sent out to a service provider or AMC for maintenance and upgrade is still owned and controlled by the organization based on the contract. So, the organization should consider the “chain of custody” risks and wipe the storage device before handing it over to a third party. In contrast, the media being exchanged or resold will renew the ownership and control in the hands of the new owner, such as a reseller. So, the organization should consider choosing a sanitization method like erasure to preserve the residual hardware value (reuse) while ensuring data destruction.
6. Verify the media sanitization and disposal process [Section 4.7]
NIST SP 800-88 guidelines recommend a verification process for media sanitization. There are two types of verification that should be taken into consideration, namely—
a) Verifying the efficiency of sanitization each time the media is wiped using the Clear or Purge technique, as some cases of Destroy do not support practical verification for each sanitized piece of media.
b) Random sample verification on a subset of the media, ideally by people who were not part of the original sanitization program
The guidelines recommend verifying the equipment, personnel, and sanitization results for failsafe assurance of the media sanitization process.
7. Maintain a certificate of media disposition [Section 4.8]
The guideline emphasizes maintaining a documented certification for every unit of sanitized electronic media, particularly those containing sensitive and confidential data. It categorically mentions the importance of automatic documentation for facilitating access to the certifications (audit trails) for physical media. As per NIST media sanitization guidelines, the certificate should include hardware and process details such as Manufacturer, Model, Serial Number, Media Type, and Source, Sanitization Method, Tool Used and Version, Verification Details, etc.
Conclusion:
The NIST 800-88 Revision 1 guidelines spell out details of how to sanitize the storage media without allowing for the possibility of data recovery, with minimum cost and in an environmentally friendly way. Organizations can refer to the three methods for media sanitization, namely Clear, Purge, and Destroy, which fit various data sensitivity levels and types of storage media such as hard drives and SSDs. These guidelines ensure compliance with regulatory standards and recommend documenting a certificate of destruction and verifying the sanitization process to safeguard sensitive information throughout its lifecycle.