South Africa, has its own data protection act, which predates the EU-GDPR. It passed the Protection of Personal Information Act in November 2013. Popularly referred to as the POPI Act or POPIA, this legislation highlights eight essential conditions that data handlers must comply with in order to protect "Personal Information (PI)". Before we see what these conditions are, let's understand the key objectives, important definitions, and other aspects of the POPIA.
Key Objectives of the POPIA
As per the official document released by the government, the purpose of the POPI Act is to:
- Guarantee the protection of PI (Personal Information) collected by private or public bodies. This condition is necessary to ensure the right to privacy that the country's constitution grants to every citizen.
- Achieve a balance between the right to privacy and other rights. Other rights include access to information and the free flow of information within national borders and beyond.
- Establish legal requirements following international standards to regulate the processing and use of PI.
- Providing rights and remedies to individuals for redressing misuse of their PI in manners contrary to the provisions of this law.
- Establish mechanisms, both voluntary and obligatory, to ensure the robust implementation of this law.
What Constitutes "Personal Information" (PI)?
Page 14 of the document containing the entire text of POPIA defines PI as any information that makes it possible to identify a natural person. In specific cases, it also implies a juristic person.
A juristic person is an organization recognized by law to have rights and responsibilities like a human individual. For example, a university can be a juristic person since it has the right to own property, etc.
As per the POPI Act, personal data includes, without being limited to, the following:
- Demographic Details include Name, Age / Date of Birth, Sex, Racial-Ethnic Origin, Language, Religion, Nationality, Color. Gender Identity. Sexual Orientation, Marital status, Pregnancy, Cultural Practices
- Contact Details include Physical Address and Location, Email Address, Telephone Number or Any other information that facilitates identifying the person's contact details in the real or virtual world
- History means Educational, Employment or Financial
Medical history, including mental and physical health & wellbeing
- Beliefs, Opinions, and Preferences of the person or about the person
- Biometric Information
- Private and Confidential Correspondence, including further correspondence that can reveal the content of the original correspondence and the purpose.
What does the "Processing" of PI Mean?
"Processing" of PI means collecting, storing, using, modifying, or destroying PI. The processing may happen manually or in an automated manner.
"Data Subject" and Related Terms
The "data subject" is the person whose information is collected and processed. De-identification of the data subject implies that any information that can identify the person gets irretrievably removed.
Another essential term in this context is "Unique Identifier". That is an identifier that a responsible party assigns to a data subject.
"Responsible Party": Who All Must Comply?
A "Responsible party" is any private or public authority that determines how and why any PI needs to be processed. Whether it's an individual a company, or some governmental outfit - they qualify as a "responsible party" when handling PI. A responsible party may function independently or in collaboration with others. However, the legal responsibilities for PI compliance remain unaltered.
The Eight Conditions of POPIA: What You Must Comply With
It is vital to clearly understand the eight foundational principles of the Act to attain compliance with POPIA. These principles determine when the processing of PI is within legal parameters.
Condition # 1. Accountability
The individuals or organizations handling PI are accountable for ensuring compliance with the POPI provisions. This condition applies both to the decision to process the PI and to the process of doing so.
Condition # 2. Processing Limitation
- PI processing must comply with the POPIA
- The process of handling PI must ensure that the person's privacy remains unaffected and the legitimate interests of the data subject remain protected.
- PI processing should always apply the principle of minimality. The implication is to use PI, which is strictly necessary for the stated purpose.
- Get consent to use PI from the data subject or a competent person when the data subject is a minor below 18 years of age. Maintain proof of consent.
- The data subject can object to the use of PI and withdraw consent at any point in time. Once that happens, the processing of such PI must stop.
- Collect data directly from the data subject unless you have their consent to collect it from a third party.
Note: There is no need to observe this condition for handling PI, which the data subject has willingly made available on public platforms. This condition also does not apply when collecting PI from a third party is necessary for court proceedings or executing a public duty.
Condition # 3: Purpose Specification
You can collect PI only for an expressly stated purpose. All data subjects must be aware of that purpose and agree with it. The time limit is another vital feature to remember. You can hold PI for only as long as you need it for the stated purpose. You must delete, destroy, or de-identify the data after the required time in a manner that makes it irretrievable.
Condition # 4: Further Processing Limitation
You cannot process PI except for the stated purpose for which you collect it, for which you have the data subject's consent. Processing for any additional purpose needs consent from the data subject.
The only exceptions are:
- If processing PI beyond the stated purpose is a legal requirement
- Such processing is necessary for national security.
Condition # 5: Quality of Information
The PI you collect and process with the data subject's consent must be accurate, complete, up-to-date, and not misleading.
Condition # 6: Openness
This condition relates to the processing of the PI collected with the consent of the data subject. A data handler must maintain robust documentation of the data processing. The data handler is also responsible for informing the data subject about:
- The data handler's name and address: this refers to the body collecting the information, not the individual
- The purpose of collecting the data
- The law and the legal provisions that allow you to collect information
- Where you collect information and where you do not
- The source of your information
- Whether sharing information is obligatory or voluntary
- The consequences of the data subject refusing to share the information
- If and when you intend to share the information with a different country
The responsible party must share all this information before collecting personal data. Also, the responsible party must have a privacy policy.
Condition # 7: Security Safeguards
This condition details the necessary measures to protect the safety and security of the PI. To comply, you must:
- Conduct a risk assessment
- Apply and maintain security measures to address the risks identified
- Verify the efficacy of the measures taken
- Ensure regular updates
Any third party handling PI for the responsible party needs to have a contractual obligation to notify the responsible party if any data breach happens immediately. If there is a data breach, real or suspected, the responsible party should immediately:
- Notify the Regulator in writing
- Notify the data subject/s in writing
Important Note:
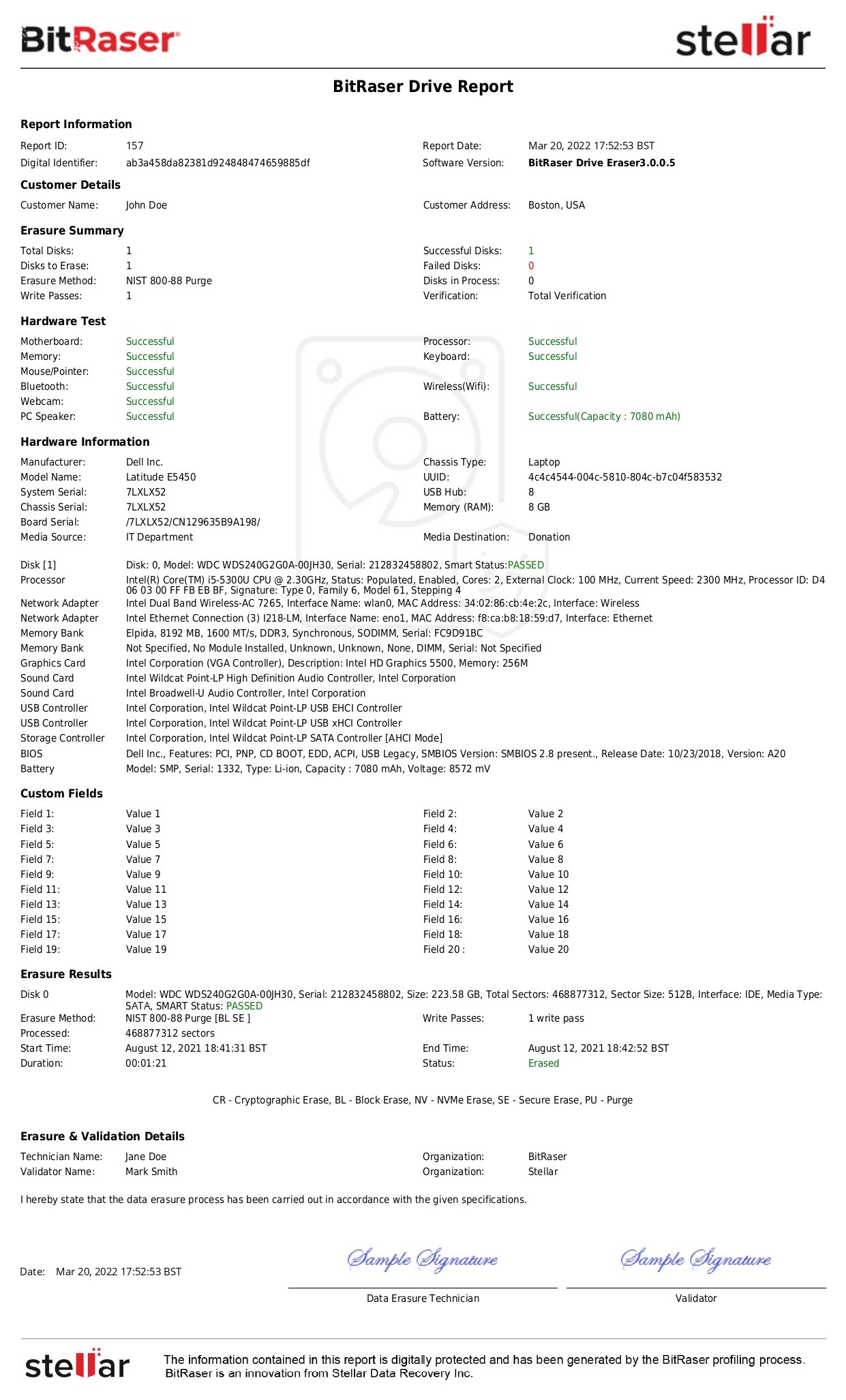
"Residual data" inside a used storage device poses a significant risk of sensitive data leakage. Residual data is the information that remains inside the storage media after deletion, formatting, or factory reset actions.
This residual information, often comprising sensitive data, is at constant risk of a breach; threat vectors like data brokers and illegal data miners can retrieve sensitive data using common recovery techniques, making you liable for the POPI Act violation.
This data breach risk can materialize when a used device changes the primary custody through events like resale, return of leased hardware, internal reallocation, exchange, donation, or disposal etc.
Systematic data erasure is an effective solution to mitigate this data breach risk through the permanent destruction of sensitive and redundant personal information in line with regulations like the POPI Act, GDPR, etc.
Related read: Meet GDPR Compliance with Secure Data Erasure
|
Condition # 8: Data Subject Participation
This condition details the rights of the persons whose information gets collected. A data subject has the right to access the collected PI. A data subject can also request correction, completion, or updating of collected information. Part B of Condition 8 prohibits the processing and using of special personal information such as philosophical & political beliefs, race, ethnicity, medical records, etc. Part C relates to the PI of children.
Who must comply with POPIA and Exemptions?
As already explained, POPIA applies to all individuals and organizations collecting and using data, especially for commercial purposes.
The exemptions mentioned in the law relate to four areas:
- PI processed for personal reasons.
- Data that has been irretrievably de-identified
- Data that a public body needs to process for law enforcement, judiciary, or national security purposes.
- Data is what the Cabinet and its committees or the Executive Council of a province need to process.
Offences & Penalties Under the POPI Act
Failure to comply with the Act can have severe consequences. The following are the critical offences outlined in Sections 100 – 106 of the POPI Act:
- Hindering, obstructing, or illegally influencing the Regulator
- Failing to fulfil an enforcement notice
- Offences by witnesses, such as failing to attend hearings
- Illegal Acts in regard to the account numbers
Violation of the Act can lead to a penalty of up to ZAR10 million in fines ten years imprisonment, or both.
Status of the POPI Act in 2020
Sections 39-54 of the POPIA deal with the appointment of the Information Regulator. These became effective in April 2014.
The Information Regulator as a body takes the responsibility of:
- Educating all stakeholders about the POPI Act
- Monitoring and enforcing compliance
- Conducting the research relevant to implement this law effectively.
- Facilitate cross-border cooperation regarding personal data security
On September 7, 2016, the National Assembly of South Africa approved the appointment of members to the Information Regulator. On December 1, 2016, the Information Regulator, along with two full-time and two part-time members, were appointed.
All the other sections related to the core provisions of the law, as detailed above, became effective on July 1, 2020. These sections are 2-38, 55-109, 111, and 114(1), (2), and (3)
Section 114(1) of the POPIA stresses that all public and private bodies must comply with the law by July 1, 2021.
Sections 110 and 114 (4) will become effective from June 30, 2021. The enforcement of these sections involves amending the Promotion of Access to Information Act (PAIA) 2000. Such an amendment is necessary to transfer certain functions of the PAIA from the South African Human Rights Commission to the Information Regulator.
Conclusion
The POPI Act remains the final word for public and private entities operating and handling personal information in South Africa. The law has strict mandates for governing the processing of PI, including its collection, storage, use, modification, and destruction.
To attain POPI compliance, you - as an organization - need a 360-degree view of how data enters and leaves your custody. Meeting the eight conditions outlined in this article is crucial for attaining compliance with POPIA. In a nutshell, strong governance, from data acquisition, storage, & use to modification and de-identification, is the foundation for POPIA compliance.