Summary: Media sanitization is of paramount importance for IT organizations because of the rising concerns around data privacy, data security, and regulatory compliance. The NIST Data Erasure Standard highlights three methods for media sanitization Clear, Purge, and Physical Destruction. In this blog, we discuss how data erasure software can use this secure erasure method to sanitize a vast variety of storage media as well as the key considerations to keep in mind.
Media sanitization is a core competency for IT organizations in the context of data privacy, data security, and regulatory compliance. Growing concerns about data privacy along with media proliferation have turned data sanitization into a critical business need.
There are various information destruction standards today - each with specific methods and guidelines - to serve the media sanitization needs. For instance, NIST Special Publication 800-88 –laid down under the Federal Information Security Management Act of 2002– outlines Clear, Purge, and Physical Destruction as the 3 methods for media sanitization. The NIST data erasure standard is a secure erase method that can be used to sanitize a vast variety of media including ATA hard disk drives and SSDs, mobile devices, USB removable media, optical media, etc.
How do NIST Clear and Purge methods erase ATA hard disk drives and SSDs?
NIST Clear and Purge are the preferred methods for sanitizing media (wherever feasible & sufficient). That's because both Clear and Purge methods rely on logical techniques – overwrite, block erase, and cryptographic erase – to sanitize the media. So, there's no e-waste generation, and also the storage media can be reused.
The following section outlines the specific techniques within NIST Data Erasure Standard:
1 - NIST Clear techniques for erasing hard disk drives and SSDs:
The NIST Clear method uses standard read/write commands, techniques, and tools to overwrite all the user-addressable locations including logical file storage locations on an ATA hard drive or SSD with non-sensitive data (binary 1s and 0s).
The Clear pattern for media overwriting should include at least a single write pass with a fixed data value such as all zeros. Multiple write passes or values that are more complex may optionally be used.
Note: Overwriting on SSDs (flash storage) may reduce the effective lifetime of the media. Also, it may not sanitize the data in unmapped physical media.
2 - NIST Purge techniques for erasing hard disk drives and SSDs:
The NIST Purge method involves Overwrite, Block Erase, and Cryptographic Erase as the logical techniques for sanitizing ATA hard disk drives and SSDs.
The Purge method uses the overwrite EXT command to overwrite – i.e. apply a single write pass of a fixed pattern (all 0s or a pseudorandom pattern) – on ATA hard disk drives. Optionally, it may apply three total write passes of a pseudorandom pattern so that the second write pass is the inverted version of the original pattern.
Block Erase is the secondary erasure method for SSDs, which "electrically" erases each block by using internal SSD functions. After successful implementation of the block erase command, the method applies binary 1s across all the user-addressable locations on the storage media and then repeats Block Erase.
NIST Purge also specifies the use of the Cryptographic Erase command to sanitize ATA hard drives and SSDs that support encryption. Cryptographic Erase can be optionally accompanied by a single-pass Overwrite, Secure Erase, or Clear techniques, based on the media support.
Key Considerations for NIST Clear and Purge Methods
- Verify the sanitization technique:
It is important to verify the efficacy of Clear and Purge techniques. For instance, for the 3-pass ATA sanitize overwrite procedure with the invert pattern, the verification process would simply look for the original pattern.
- Reset the storage device's configuration capabilities:
Storage device configurations such as Host Protected Area (HPA), Device Configuration Overlay (DCO), or Accessible Mac Address may hinder the ability to access the entire addressable area of the storage media. Therefore, these should be reset before implementing the sanitization technique.
- Verify the Cryptographic Erase command individually:
Verify and ascertain successful completion of Cryptographic Erase before implementing additional sanitization techniques such as Clear or Purge. This is because not all implementations of media encryption are suitable for Cryptographic Erase as a Purge mechanism.
- Evaluate media-specific use of ATA Secure Erase:
ATA Secure Erase serves only as a 'Clear' mechanism for flash memory, so there is a possibility that sensitive data may remain in areas such as spare cells that have been rotated out of use. So, use the SECURITY ERASE UNIT command only after ascertaining its efficacy, based on the type of media.
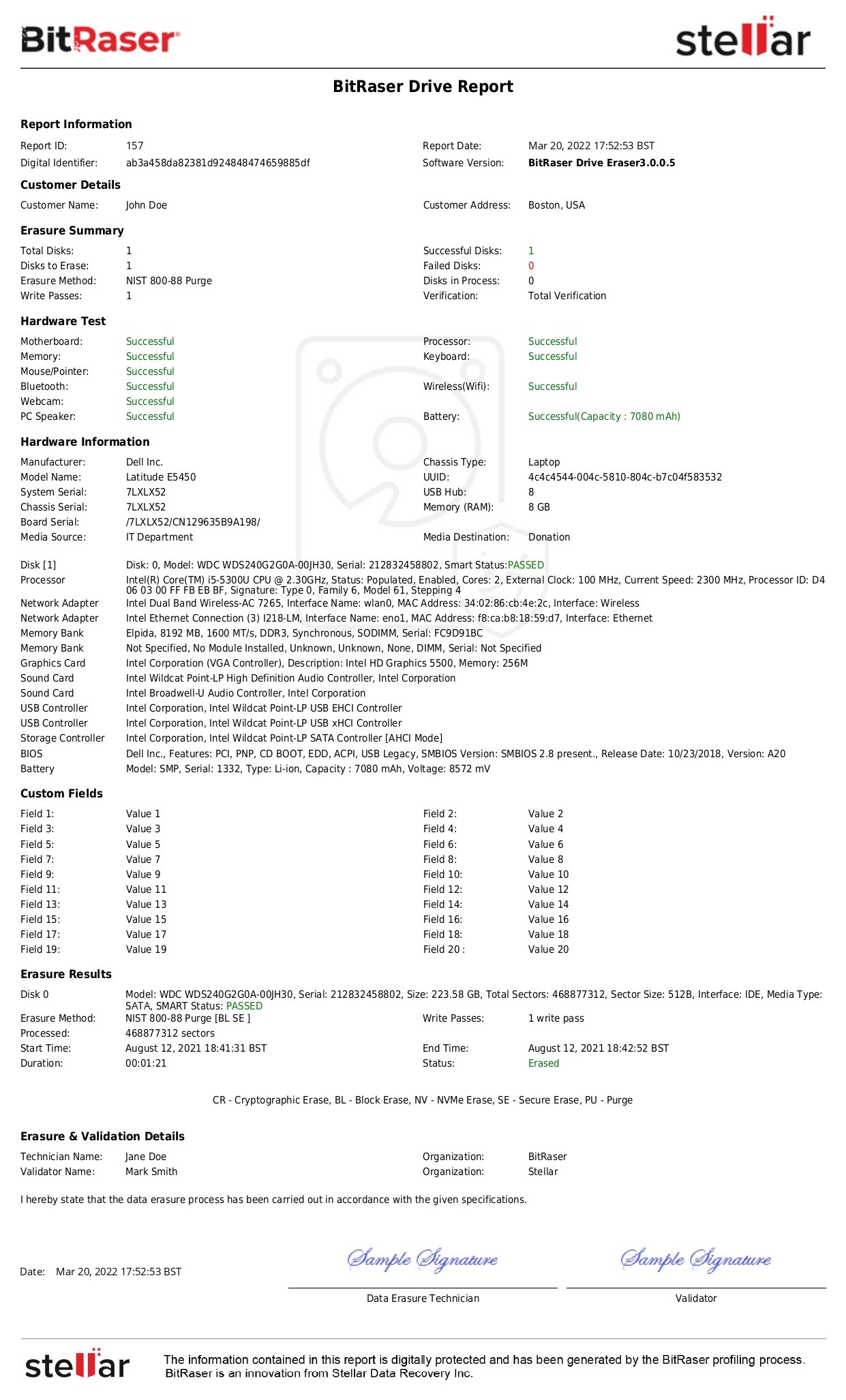
How does Data Erasure Software Help Implement NIST Clear and Purge?
A Data erasure software like BitRaser can perform media sanitization by overwriting the data, based on NIST Clear and Purge methods. This plug-and-play data erasure tool can add up to 5 customized erasure algorithms. It also provides tamper-proof audit trails to help businesses attain compliance with data security & privacy standards such as SOX, GLB, HIPAA, ISO27001, EU-GDPR, and PCI-DSS.