Every IT asset, including data storage hardware, entering an organization’s custody transitions through discrete lifecycle stages. These stages include procurement, allocation, use, reallocation, repair and upgrades, and disposal through transactions like hardware exchange, refurbishment, resale, return (of leased assets), donation, recycling, etc.
Safe data disposal is a critical need across the storage device lifecycle stages. Data disposal laws today require the permanent destruction of data (sensitive business information including customer data) accumulated over a period on these devices. Storage hardware such as Network Attached Storage (NAS), rack-mounted servers, external hard drives, desktops, and laptops, etc., can gather terabytes of confidential and personal data in their lifetime. This information, under the purview of overarching data protection laws like GDPR, CCPA, and others can pose severe risks to the custodian organization in the eventuality of a data breach or leakage incident.
This article outlines the data breach risk implications emerging due to unsafe data disposal for organizations, and key considerations to attain compliance and safe disposal of personal data.
What are Common Reasons for Unsafe Data Disposal?
There could be multiple reasons why an organization may fail to attain safe disposal of personal data based on technical and non-technical reasons. For example, a technical reason could be that an organization may rely on degaussing without adequately considering the degaussed magnetic media’s field strength— a fundamental consideration when disposing of data using degaussing. Consequently, the degaussed magnetic media, such as a hard disk drive, contains “residual data,” i.e., unaccounted sensitive information at constant risk of leakage and misuse. Unknowingly, the residual data on the insufficiently degaussed hard drive is potentially recoverable using forensic, in-lab data recovery techniques, causing data breaches to the organization.
A non-technical reason could include lapses in an organization’s due diligence while the storage device is transitioning the chain of custody. For example, gaps in vendor management practice can lead to ineffective data disposal or inadequate/missing audit trails, resulting in data breach incidents, haunting the organization several years later. The Morgan Stanley data breach episode, involving the reporting of two data breach incidents that held the banking behemoth accountably, illustrates the risks and penalties of unsafe data disposal.
Notably, “lack of awareness” concerning residual data’s existence and risks is a root cause of why organizations may fail to sanitize a media per the data disposal benchmarks. The World’s largest Residual Data Study of 311 used devices illustrates residual data prevalence and its imminent threats. The study analyzed used hard drives, smartphones, and memory cards, revealing that 7 in 10 devices were vulnerable to sensitive data leakage. It found that 1 in 4 device owners had used deletion and formatting to dispose of the data, unaware that deletion & formatting does not permanently remove the data.
What are the Risk Implications of Unsafe Data Disposal of Hard Drives & other storage devices?
Failure to use safe data disposal methods like using data erasure software can result in a data breach with risk implications such as financial fraud, IP theft, brand damage, lawsuits, and penalties, resulting in significant monetary losses. A study by Ponemon Institute informs that the global average cost of a data breach for companies was $3.86 Million in 2018, with a 6.4% growth over the preceding year. The following sections outline the major risks of unsafe data disposal and their financial repercussions in terms of penalties.
Legal Penalties
Violation of data protection laws such as EU-GDPR, GLBA, and CCPA and failing to comply with what data disposal laws require can trigger legal proceedings with extensive penalties. For instance, HIPPA violation could result in fines of up to $50,000 per violation for willful neglect, with a maximum of USD 1.5 Million per year for violations of an identical provision. Similarly, violating EU-GDPR could result in fines of up to 4% of annual global turnover or €20 Million.
Loss of Goodwill & Market Share
A data breach incident can dramatically affect a company’s market share, causing reputation loss and razing its competitive advantage. For instance, theft of customer information could jeopardize the reputation of businesses like banking institutions, e-commerce websites, social platforms, and the likes. IBM’s 2018 Data Breach study informs that digital businesses with 1% customer churn due to a data breach suffered a loss of $2.8 Million which could jump to $6 Million for a 4% or higher churn rate.
Financial Fraud
Financial frauds are on the rise, with more transactions going digital. Breaches of PII such as social security number, mobile number, name, and financial information like online banking credentials and credit card details can incur a high cost for the business. For example, fraudulent credit card transactions hold the eCommerce merchant liable to bear the loss after the card owner files for a chargeback. The average cost of credit card fraud for the merchant equals $200 per compromised cardholder.
What are Critical Considerations for Safe Data Disposal?
As an organization, you need to make a few fundamental choices to guide your data destruction strategy. These choices include —
- Data Destruction Technique
- Data Destruction Location: Onsite vs. Offsite
- Choosing Responsible Entity: DIY vs Service Provider
1. Data Destruction Technique
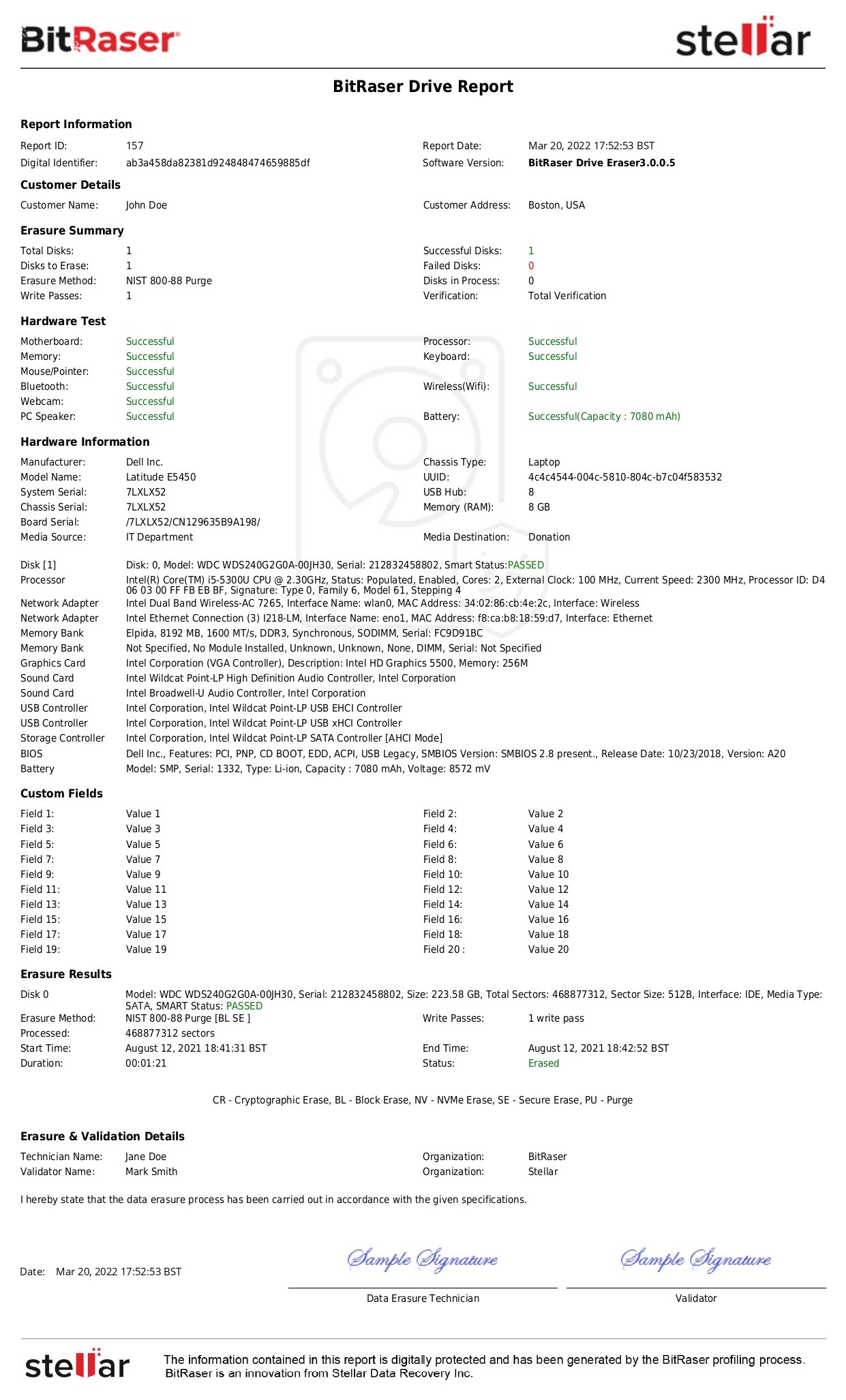
Broadly, there are three data disposal techniques: Overwriting (Data Erasure), Degaussing, and Shredding. These techniques use the Clear, Purge, and Destroy methods explained in the NIST SP 800-88 Guidelines. Choosing the appropriate data destruction technique based on the media type is crucial for the effective and safe disposal of data. Do read our article on data destruction techniques for an in-depth insight into this subject while choosing the appropriate technique.
2. Data Destruction Location: Onsite vs. Offsite
Organizations can perform data disposal on-premises (onsite) or off-premises (offsite) with consideration of the applicable advantages and disadvantages. You may see the comparison below to understand the effectiveness and choose accordingly.
Onsite vs Offsite Data Disposal: Comparison
| Parameter |
Onsite Data Destruction |
Offsite Data Destruction |
| Effectiveness |
Highly effective if done using the appropriate method w.r.t the storage media type. |
Highly effective, considering offsite data disposal is done at a specialized service facility. |
| Data Leakage Risks |
Low Risk of data leakage as the media remains onsite. |
The potential risk of data leakage while the media is in transit to the third-party service facility.
|
| Cost |
Onsite data disposal can be affordable and cost-effective if done using data erasure software like BitRaser with pay-per-use licensing. Costs can increase with the involvement of degaussing unit, shredder, & specialized personnel. |
Offsite data disposal, being a contracted service, is typically costlier. However, organizations with larger consignments can avail lower per-unit costs with economies of scale. |
3. Responsible Entity: DIY vs Service Provider
An effective data disposal strategy is also about defining who performs the data disposal job effectively. The choice is between ‘Data Destruction’ by specialized commercial service providers known as ITADs or Do-It-Yourself using a secure data erasure software to get rid of data securely. For low volumes of devices to be erased organizations may do it themselves. However, for large volumes of devices to be refurbished, the organizations may rely on service providers for IT Asset disposition.
Conclusion
Safe data disposal is critical for organizations to safeguard them from data leakage & risk implications like fraud, customer loss, and litigation. As understood in this article, all storage devices transition through discrete lifecycle stages in the organization’s custody before leaving its possession. Therefore, the organization needs to designate checkpoints, accountabilities, and actions for all these stages as the starting point to attaining the expected data disposal outcomes. Choosing the right methods for data disposal as per the storage media type, data destruction partner & location are important factors for defining the data destruction strategy. Careful and informed decisions based on these considerations can help organizations achieve their media sanitization goals as per the requirements of data disposal laws.