R2v3 — the latest version of the Responsible Use and Recycling (R2) standard, introduces several new requirements to augment the outgoing R2:2013 version. These requirements span across areas like R2 facility audit for used electronics, ongoing public communication of additional locations, periodic risk evaluation, visual inspection of electronic equipment, etc. Additionally, R2v3 also enhances the existing requirements on aspects such as documenting the scope of the operations, evaluating and sorting the equipment, monitoring compliance, etc.
What’s New in R2v3? Must-Know Compliance Checklist
This section outlines the new inclusions in R2v3 that had no precedence in R2 ver. 2013. These 65+ new requirements are covered in various sections of the official R2 version 3.0 documentation (© SERI, 2020: The R2 Standard by SERI Version 3), including scope, tracking throughput, data security, facility requirements, etc. Meeting these new requirements is critical to attaining R2v3 compliance.
1. Scope – Auditing & Public Communication of External Locations, Processes & Activities
R2v3 mandates auditing and certifying all the electronic equipment, components, and materials managed at the R2 facility. It also brings all processes and activities, including external processes & locations in control of the R2 facility, in the purview of audits and certification. R2v3 necessitates the facility to maintain and publicly communicate, on an ongoing basis, the current listing of all its owned and/or operated “non-R2” locations used for electronics recycling. Further, the latest R2 standard prohibits R2 certification of any organization listed on the SERI website for deceptive, fraudulent, or illegal acts within the past 24 months.
Refer to sections 1(a), 1(c), & 1(d) of R2v3 Changes and Highlights Summary v1.
2. EH&S Management System – Risk Exposure, Visual Inspection, and Sanitization
New inclusions in the Environment, Health, and Safety (EH&S) Management System section of R2v3 bring enhanced focus on risk exposure, visual inspection, and sanitization. Firstly, it mandates the R2 facility to periodically assess the risk of exposure to hazardous substances like mercury, lead, cadmium, etc., due to the processing or handling of electronic equipment. The requirement also necessitates visual inspection of all electronic devices and components for damage or other issues that could harm the environment, health, and safety of personnel.
Refer to sections 3(d) - 3, 4, 6, &7 for more information.
3. Legal Requirement – Child Labor, Prison Labor, & Non-Discrimination
The new requirements direct all R2 facilities to not employ child labor or forced labor in accordance with International Labor Organization (ILO). An R2 facility can employ prison labor only if done willingly, compensated, and taught the required skills for gainful employment after release. R2v3 also mandates the R2 facilities to document a non-discrimination policy stating the fair and equal treatment of all workers.
Refer to sections 4(e), 4(f), and 4(g) for details.
4. Tracking Throughput – Track, Manage and Maintain Accurate Records
R2v3 guidelines obligate the R2 facility in control of electronic equipment, components, and materials to “track, manage, and maintain accurate records of the quantity of R2 Controlled Streams.” It necessitates maintaining the total inventory levels within the defined limits for the R2 facility’s legal requirements, closure plan, and financial assurance. This section also directs the facility to not store R2 Controlled Streams or materials with a negative value for more than one year.
Check sections 5(b) of R2v3 Changes and Highlights Summary v1.
5. Sorting, Categorization, and Processing
R2v3 introduces extensive requirements in this section, spanning areas such as documentation, categorization, management of R2 Controlled Stream, process, etc. It directs R2 facilities to develop and maintain documentation to evaluate, sort, and categorize electronic equipment, components, and materials. The categorization should be identified with the facility’s R2 equipment categories, and the facility should manage the equipment as R2 Controlled Stream as per R2 requirements. Further, the process requirement categorically states that “all equipment and components shall be evaluated for data, including connected user accounts and services, and identified with the corresponding data sanitization status.”
Refer to sections 6(a), 6(b), 6(d), and 6(e) for more details.
6. Data Security – Data Sanitization, Access Control, and Notifications
R2v3 introduces nine new requirements within the Data Security section, emphasizing a documented data sanitization plan, procedure, and policy. The following are the new inclusions:
a) Documentation – The latest guidelines instruct R2 facilities to document and maintain a data sanitization plan to define security controls for data protection, types of data storage devices and data, network services that could auto-populate the sanitized data, etc. Other mandatory elements in the documentation include data sanitization methods for each storage device type, timelines for sanitization, details of downstream vendors that perform data sanitization, etc.
The R2 facility must draft a data security policy that prohibits unauthorized individuals from accessing or handling the data-bearing devices and assigns a Data Protection Representative with the overall responsibility for data security and regulatory compliance. The policy mandates reporting of known and suspected data breaches to the Data Protection Representative.
Read sections 7(a) 1 & 2 of R2v3 Changes and Highlights Summary for more details.
b) Security – R2v3 data security requirement directs R2 facilities to develop and implement “levels of security authorizations to control access” based on the equipment type, data security, and other facility-specific needs. It mandates identifying and labeling the controlled areas with warning signage and compels the R2 facility to maintain written acknowledgments from individuals granted security authorization.
Refer to sections 7(b) 2, 3, 4, 5, and 6 for more details.
c) Process & Notifications – The R2 facility needs to provide the equipment supplier confirmation of the receipt of data-bearing equipment, data sanitization method, and the party (internal or 3rd-party) responsible for sanitizing the storage media. Further, the R2 facility shall maintain a process to notify the supplier concerning any changes in downstream vendors and security or data breaches.
Refer to sections 7(c) and 7(d) for more details.
7. Focus Materials
New requirements in this section include the need for demonstrated proficiency, planned methods, and capacity to process each type of electronic equipment containing focus materials. The R2 facility is obligated to manage all electronic equipment, components, and materials in line with R2 core requirements to ensure legal compliance, environmental protection, and worker & public health safety.
Read sections 8(a) – 1, 2, 3, and 8(c) for in-depth understanding.
8. Facility Requirements
R2v3 obligates the R2 facilities to perform all their processing operations indoors unless a facility has determined the outdoor processing risks and placed controls to contain them. Further, an R2 facility now does not need to have financial instruments for assuring closure due to abandonment if it meets the following conditions:
- The total cost of closure is less than US$ 10,000
- The facility size is less than 1000 m2
- The facility does not accept equipment or materials containing mercury, CRT glass, lithium primary batteries, or polychlorinated biphenyls.
- Refer to sections 9(a) and 9(f) for more details.
9. Transport
The transportation section in R2v3 now includes a requirement for accurate shipping documentation. R2 facilities need to label their shipments accurately and use codes, descriptions, and declarations in accordance with the regulatory guidelines.
R2v3 Process Requirements – Downstream Recycling, Data Sanitization, & More
Aside from the main sections, the latest guideline also incorporates new “process” requirements extensively in appendices A, B, C, D, E, and F. The following is a highlight of these new process requirements:
a) Downstream Recycling
The R2 facility needs to track and demonstrate the complete downstream recycling chain of all R2 Controlled Streams to final disposition. It also needs to verify that R2 Controlled Streams are received at the downstream vendor’s facility.
b) Data Sanitization
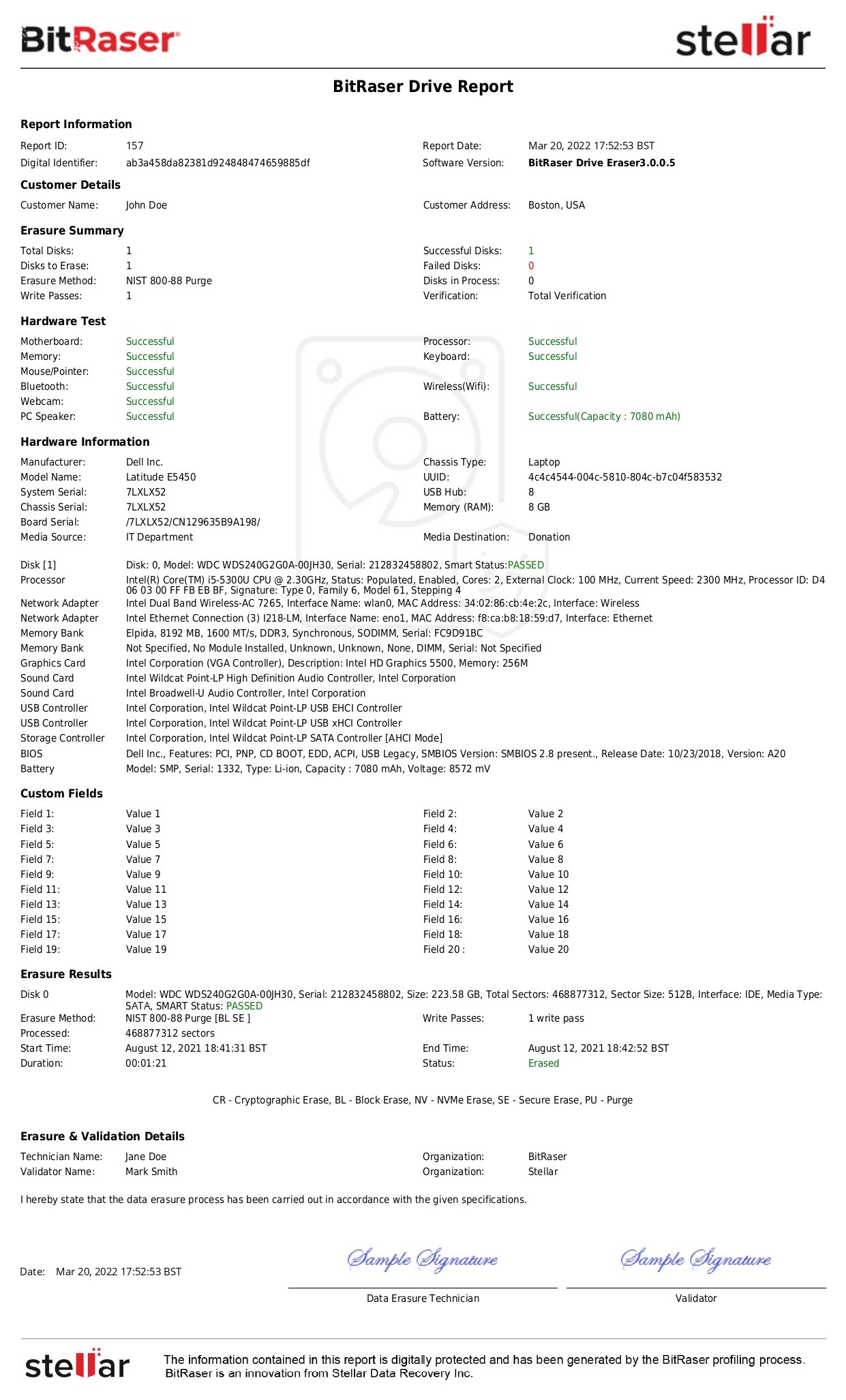
The facility must remove and destroy all markings that could associate a device with its previous user. Data storage devices requiring physical sanitization must be destroyed as per the described physical destruction methods or in accordance with NSA Storage Device Sanitization Manual. The facility needs to maintain video recordings of the physically destroyed media for at least 60 days. For logically sanitized storage media, the facility needs to maintain electronic records of data sanitization generated using the data erasure software. The software should be configured to sanitize all user-addressable locations.
Refer to Appendix B (4), B (6-14), and B (16, 17) for more details.
c) Test and Repair
The new inclusion for the Test and Repair requirement in R2v3 states – “An R2 Facility certifying to Appendix C – Test and Repair shall also be certified, by an accredited Certification Body, throughout the duration of its R2 certification, to an approved quality management system (QMS) standard with a scope that includes all the equipment, components and processes to which this Appendix C applies.”
It also obligates the R2 facility to demonstrate the actions to test and verify the equipment's safety for reuse.
Further reading: R2v3 CHANGES AND HIGHLIGHTS SUMMARY Version: 1
R2v3 Certification: Positive Impact on ITADs
- R2v3 certification as the highest quality standard in the sustainability space can position ITAD businesses as trusted and responsible leaders.
- R2v3 certified ITADs could position themselves as thought leaders on responsible recycling and reuse of electronics.
- R2v3 is a seal of approval to ensure that ITADs adhere to the highest standards for data destruction and sanitization.
R2v3 Recycling Certification: Key Benefits
- Endorses safe and efficient reuse of electronic materials and equipment
- Protects downstream control of the recycling chain
- Reduces risks to the environment and public health
- Validates adherence to local and international laws
- Supports OEMs with due diligence for end-of-life electronics products
- Instills confidence in public via certified third-party assessment
Conclusion: Summarizing The Changes
A major difference between R2v3 and R2:2013 is that the new version requires R2 facilities to maintain more granular details such as the scope statement, process requirements, list of all related locations, etc. The updated standard strengthens the data security and sustainability requirements while permitting innovation to attain better outcomes. The changes include safer handling of material flowing to downstream vendors concerning data protection and environment, health, and safety (EHS) needs.
R2 facilities have to document and maintain a plan and procedure for data sanitization. In addition, they have to maintain a written data security policy. All the workers at the facility should be given regular training and scrutinized for compliance with data security policies and procedures. Besides, R2 facilities have to implement a data security program to control access to the facility based on the type of electronic equipment, the sensitivity of data on the storage devices, etc.